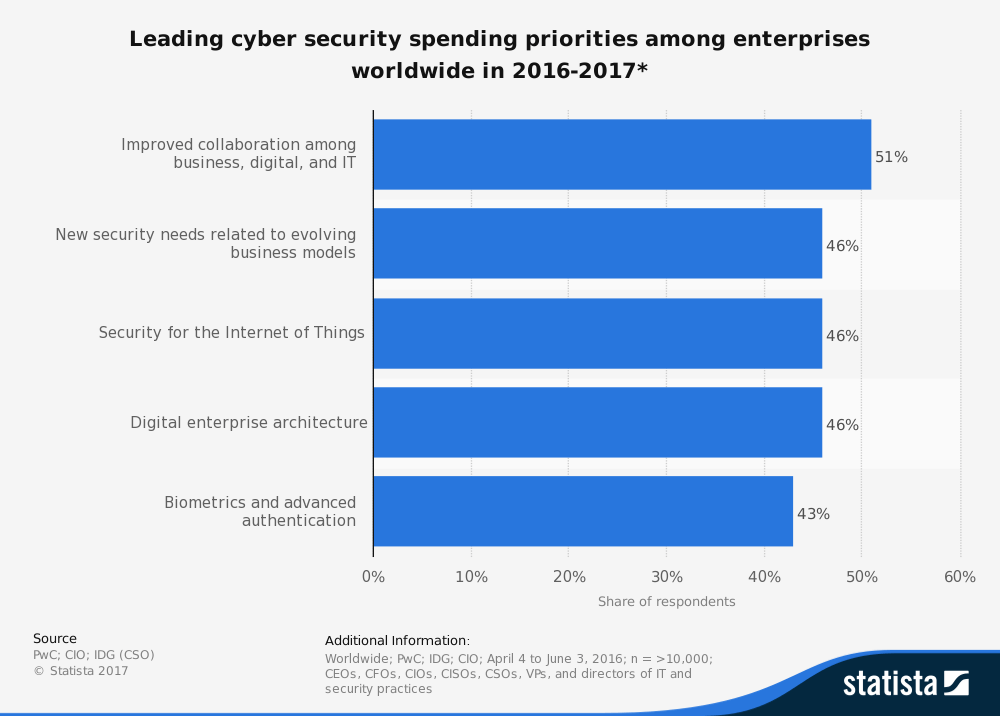
As shown in figure 1, leading cyber security spending priorities for enterprises worldwide span five main areas from 2016 to 2017. Improved collaboration is the top spending priority for C-level executives and IT and security directors.
Addressing IT risks before incidents occur
A related Forbes publication concurs that Chief Executive Officers (CEOs) have always had very broad responsibilities. However, with the ever-present threat of information security breaches, CEOs are becoming increasingly responsible for their organizations’ overall security. Failure to take responsibility could cost millions, and often also results in a never-ending public relations nightmare, notwithstanding an exodus of customers and clients.
That means organizations need to address IT security risks before these incidents occur. This includes identifying key threats, reviewing existing security vulnerabilities and challenges to the agency’s data, enforcing risk management processes and common control frameworks, executing incident management processes (when crises occur), and empowering experts to maintain regular communications about security-related issues.
Being informed about security risks is not enough, though. Organizations need to align their security intelligence plans with those they serve as well as with their employees. Integrating three-step security protocols, for example, can help prevent a password security breach, which is one of the most common methods used by hackers to gain access to a company’s internal system.
Apply predictive analytics to detect advanced threats.
While defending company systems is crucial, the most innovative systems need to go a step beyond defense and apply predictive analytics that detect any advanced, persistent threats. Such integrated data analytics are capable of identifying previous breach patterns, and are then able to predict potential areas of attacks.
Security intelligence should have five capabilities:
- Real-time flow analytics that track and monitor user behavior, social media usage, and mobile and cloud activity
- Predictive analytics and pre-exploit awareness to identify unusual trends and patterns in behavior
- Anomaly detection to uncover activities and behaviors beyond what’s expected
- Data source integration and visualization, with collaboration among various data sources to spot threats
- Management of all endpoints, including mobile devices.